What is Cyber Fraud in 2025: Your Essential Guide to Staying Safe Online
September 23, 2025ICS Cyber Resilience: Building Business Continuity Beyond Firewalls
September 12, 2025Post Quantum Cryptography: A Complete Guide for Business Leaders
September 6, 2025The Hidden Costs of Pirated Downloads: Why ‘Free’ Isn’t Free
September 2, 2025What is Cyber Fraud in 2025: Your Essential Guide to Staying Safe Online
Welcome to 2025. In our increasingly digital world, life online offers incredible convenience and connection. But with every step forward in technology, there’s...
ByKumar SSeptember 23, 2025ICS Cyber Resilience: Building Business Continuity Beyond Firewalls
The industrial landscape is undergoing a digital transformation that’s reshaping how we think about cybersecurity. As Chief Information Security Officers extend their purview...
September 12, 2025A Top 5 Disruptive Trend in Cybersecurity for 2025
Ever felt like you’re one phishing email away from a total digital meltdown? You’re not alone. Cyber threats are evolving fast—so fast that...
August 14, 2025Cloud Security Best Practices Every CISO Needs to Master
In today’s fast-paced digital world, businesses are moving to the cloud faster than ever. It’s like moving your entire office from a building...
August 14, 2025Third Party Risk Assessment: Vendor Due Diligence Requirements
It’s no secret that businesses today rely heavily on other companies, called “third parties” or “vendors,” to get things done. From cloud storage...
August 6, 2025Highlights
Cybersecurity in Industrial Control Systems: Best Practices & Threats in 2025
Picture this: It’s 3 AM, and your CISO’s phone is buzzing with an urgent alert. A sophisticated threat actor has infiltrated your manufacturing...
ByKumar SFebruary 3, 2025How to Send Secure Email in Outlook: A Step-by-Step Guide
In today’s digital age, ensuring the security of your emails is more important than ever. Whether you’re sharing sensitive business information, personal data,...
ByKumar SApril 25, 2025What is Cyber Fraud in 2025: Your Essential Guide to Staying Safe Online
Welcome to 2025. In our increasingly digital world, life online offers incredible convenience and connection. But with every step forward in technology, there’s...
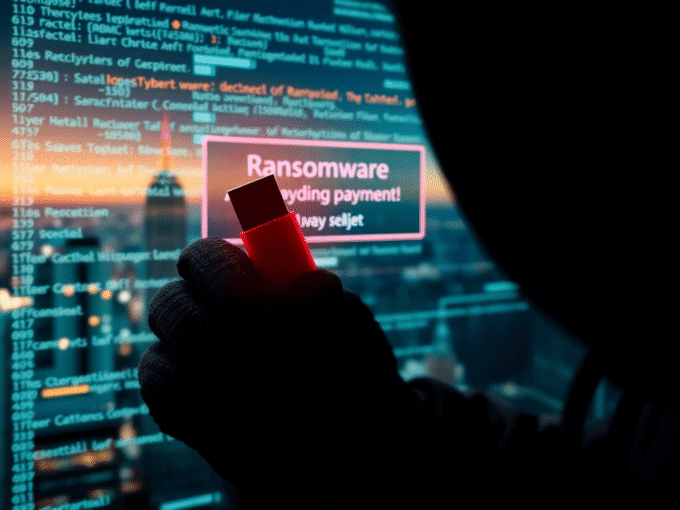
ByKumar SSeptember 23, 2025What Is Ransomware and How Does It Work?
In today’s digital landscape, ransomware has emerged as one of the most pervasive and destructive forms of cybercrime. This malicious software encrypts a...
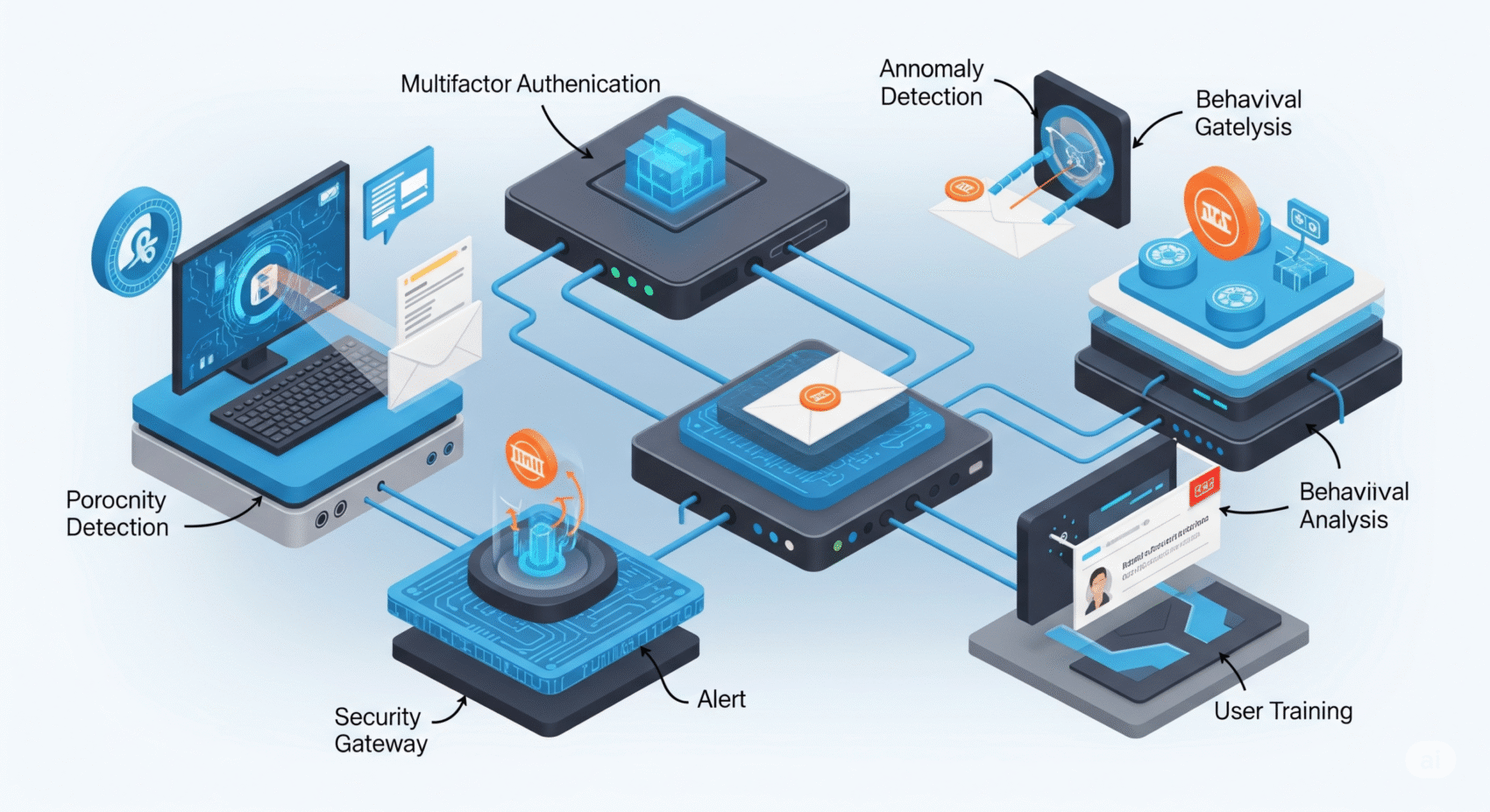
ByKumar SJanuary 6, 202510 Proven Strategies to Strengthen Digital Security Today
In today’s world, where cyber threats are becoming more and more common, protecting our personal information and company data is no longer just...
ByKumar SJanuary 13, 2025Recent Attacks
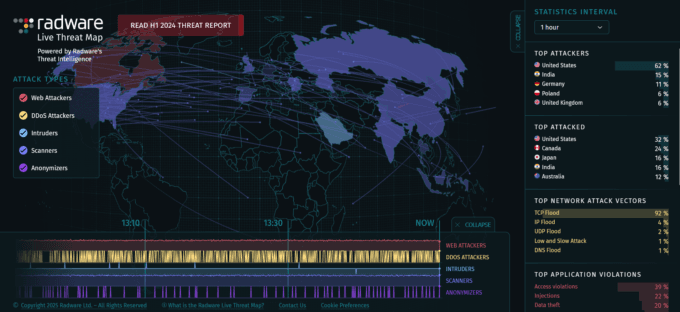
Palo Alto Networks Alarm on Rising Brute-Force Threats to PAN-OS Gateways
In a recent advisory, Palo Alto Networks revealed that it is actively monitoring Brute-Force Threats targeting its PAN-OS GlobalProtect gateways. This announcement comes...
ByKumar SApril 13, 2025Oracle Confirms Data Breach in Legacy Cloud Systems: What You Need to Know
Oracle confirms data breach that a hacker accessed two legacy, deprecated servers—not part of Oracle Cloud Infrastructure (OCI)—leaking login credentials such as usernames,...
ByKumar SApril 4, 2025Malaysia Airports Hit by Cyberattack; Hackers Demand US$10 Million Ransom
Examining the impact of Malaysia Airports Hit by Cyberattack and broader implications for critical infrastructure security.
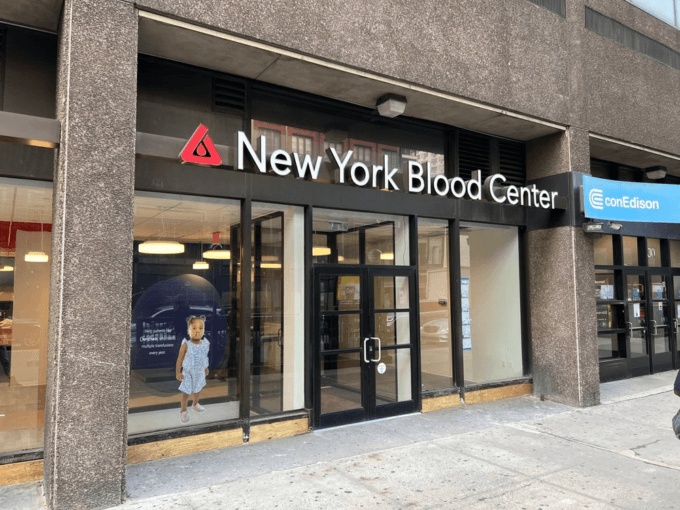
ByKumar SApril 2, 2025New York Blood Center ransomware attack – Inside Details
On January 26, 2025, NYBC detected suspicious activity on its IT systems, which was later confirmed as a ransomware attack. This breach has...
ByKumar SFebruary 1, 2025Top 11 Cyber Attacks of 2024 Worldwide: Shocking Breaches That Changed the Game
For a broader context on global cybersecurity trends in 2024, explore this insightful analysis from Cybersecurity Ventures: Cybersecurity Trends 2024. 2024 was a...
ByKumar SJanuary 27, 2025ICBC Bank Ransomware Attack Key Insights
In November 2023, the world’s largest bank by assets fell victim to a devastating ransomware attack that sent shockwaves through global financial markets....
ByKumar SJanuary 6, 2025Awareness
Subscribe to Updates
Subscribe to our newsletter to get our newest articles instantly!
Recently Updated
What is Cyber Fraud in 2025: Your Essential Guide to Staying Safe Online
Welcome to 2025. In our increasingly digital world, life online offers incredible convenience and connection. But with every step forward in technology, there’s...
ByKumar SSeptember 23, 2025WhatsApp & SMS Scams: How They Work and How to Stay Protected
Have you ever received a text message or a WhatsApp chat from an unknown number, asking for personal details, promising a prize, or...
ByKumar SJune 4, 2025ICS Cyber Resilience: Building Business Continuity Beyond Firewalls
The industrial landscape is undergoing a digital transformation that’s reshaping how we think about cybersecurity. As Chief Information Security Officers extend their purview...
ByKumar SSeptember 12, 2025Cybersecurity in Industrial Control Systems: Best Practices & Threats in 2025
Picture this: It’s 3 AM, and your CISO’s phone is buzzing with an urgent alert. A sophisticated threat actor has infiltrated your manufacturing...
ByKumar SFebruary 3, 2025